I’ve been using GnuPG since years. Well, using is too strong. I have a GPG key that I’ve created somewhen and use it once in a while when sending login credentials to other Linux people. But since Edward Snowdens NSA leaks I now get encrypted mails by non-Linux people. It is great that people are making use of strong encryption to protect their communication, but it is frightening that people have to do so because of NSA mass surveillance the complete world and violating our civil and human rights.
Anyway, one problem with GnuPG and other PKI tools is, that you should keep your private key secret. When you use more than one device to write your mails, you will run into usuability problems like I did. My main computer is my Debian box, but I use a MacBook Pro laptop with OSX very often as well. There is GPGSuite (formerly GPGMail) for OSX to pimp your Mail.app with GPG. It uses, of course, a local .gnupg/ directory and thus it would create a separate GnuPG pair of keys. But apparently I want to use my existing pair of keys – without the need to copy them over from my Linux box to my laptop.
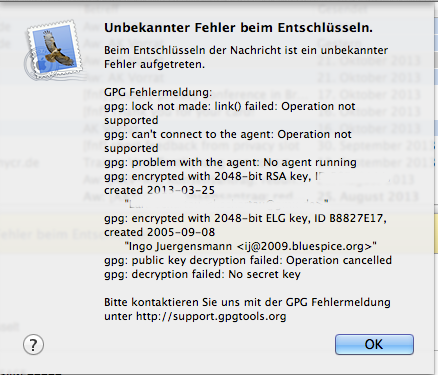
The solution would be a simple setup of netatalk to mount your home directory from the Linux box under OSX and a matching symlink to your Linux .gnupg/ directory (or even better: symlink the contents where necessary and not the whole directory). But that would’ve been too easy, I guess, because I got this error message on OSX:
So, basically this didn’t work right out of the box. Fortunately the GPGSuite support guys replied quick and solved this problem. The version they released yesterday did fix that problem, but I needed to add the following line to my ~/,gnupg/gpg-agent.conf, which didn’t exist before too:
no-use-standard-socket
With that line everything works like a charme under OSX with Mail.app using my GPG keys on my Debian box.
Use subkeys instead
This approach his it’s drawbacks; the right way to solve this problem is to use subkeys. You could write/sign emails with the laptop »on the road« (without internet access to your home computer), but if it’s stolen, you could simply rewoke the subkey and create a new one with the master key keept in your basement, without the need to rebuild your reputation in the Web of Trust.
Use an OpenPGP smartcard instead
Soft private keys are vulnerable to malware and OS bugs (which happens from time to time), so to get good protection of the private key, I would recommend using an OpenPGP smartcard instead. It works fine under Windows, GNU/Linux and Mac OS X.
Even better is to combine using a smartcard with subkeys, as per the other comment. 🙂
Isn’t copying the key on each access worse than doing it once?
If you have to copy the key on each access over the network, isn’t this worse that doing it only once? I’d also think that it is a bad idea to have the private key accessible directly via network, as a key should be ideally accessible from nowhere.
I’d rather spend time and money on the smartcard solution, as this will allow you to share the same key securely between systems.
As always: it depends.
As always: it depends.
1) I assume my home network is “safe” (at least to some degree)
2) from outside of my home network I can access that key via VPN, so it should considered safe as well
3) copying the private key onto mobile devices is a bad idea especially when the mobile got lost. Depending on your passphrase and key length it might be subject to brute force attacks.
Even better is to combine
Even better is to combine using a smartcard with subkeys, as per the other comment. 🙂
Lucas de lyon
Soft private keys are
Soft private keys are vulnerable to malware and OS bugs (which happens from time to time), so to get good protection of the private key, I would recommend using an OpenPGP smartcard instead. It works fine under Windows, GNU/Linux and Mac OS X.
Even better is to combine using a smartcard with subkeys, as per the other comment. 🙂
The solution would be a
The solution would be a simple setup of netatalk to mount your home directory from the Linux box under OSX and a matching symlink to your Linux .